Cybersecurity Trends in 2026: 10 Threats Every Business Must Prepare For


4
Cyberattacks are no longer rare incidents. They happen every few seconds somewhere in the world.
Businesses of every size — from startups to large enterprises — are being targeted by ransomware, phishing attacks, and data breaches. Many companies assume hackers only target big corporations, but the reality is very different.
Small and medium-sized businesses are now among the most common targets because they often lack strong security systems.
In 2026, ignoring cybersecurity can lead to:
- Financial losses
- Data leaks
- Business downtime
- Legal consequences
- Loss of customer trust
Understanding modern cybersecurity threats is the first step toward protecting your business.
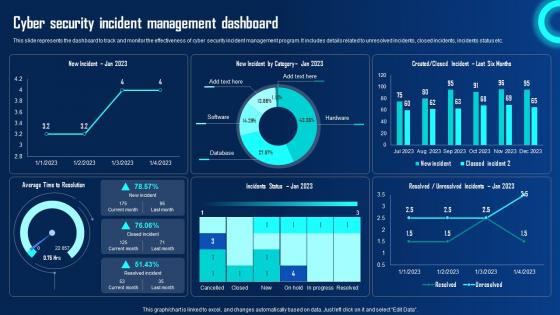
Cybersecurity in 2026: Quick Statistics
Before diving into the trends, here are some important facts that show how serious the situation has become:
- Global cybercrime damages are expected to exceed $10 trillion annually.
- A ransomware attack occurs every few seconds worldwide.
- Around 60% of small businesses shut down within six months of a major cyberattack.
- Phishing attacks account for over 80% of data breaches.
- The average cost of a data breach for businesses continues to rise each year.
These numbers show why cybersecurity is now a core business priority, not just an IT task.
10 Cybersecurity Threats Businesses Must Prepare For in 2026
Understanding these threats helps businesses build stronger defenses.
1. AI-Powered Cyber Attacks
Hackers are now using artificial intelligence to automate cyber attacks.
AI tools can:
- Scan websites for vulnerabilities
- Generate highly convincing phishing emails
- Crack weak passwords faster
- Adapt attacks based on system responses
These attacks are harder to detect because they mimic normal user behavior.
Businesses must use advanced security monitoring tools to identify suspicious activity early.
2. Ransomware Attacks
Ransomware remains one of the most dangerous cyber threats.
In a ransomware attack, hackers encrypt company files and demand payment to restore access.
Modern ransomware attacks often include double extortion, where attackers threaten to leak sensitive data if payment is not made.
Real Business Example
A manufacturing company lost access to its entire production system after ransomware encrypted its operational files.
Because the company did not maintain secure backups, operations stopped for several days. The financial losses were significant.
Regular backups are one of the most effective ways to reduce ransomware damage.
3. Phishing Attacks
Phishing attacks continue to evolve and remain one of the most common causes of security breaches.
Attackers send emails that appear to come from:
- Company executives
- Banks or payment providers
- Trusted vendors
- Government organizations
Employees may accidentally click malicious links or share login credentials.
Warning Signs of Phishing Emails
⚠ Unexpected attachments
⚠ Urgent financial requests
⚠ Suspicious links
⚠ Emails requesting passwords
Employee awareness training is essential to reduce this risk.
4. Supply Chain Cyber Attacks
Many businesses rely on third-party software vendors and service providers.
Hackers often target weaker vendors to gain access to multiple organizations at once.
If a third-party system is compromised, it can expose sensitive business data.
Companies must evaluate the security practices of vendors before integrating their services.
5. Cloud Security Misconfigurations
Cloud services help businesses store and manage data efficiently, but configuration mistakes can expose sensitive information.
Common issues include:
- Incorrect access permissions
- Weak password protection
- Lack of encryption
- Poor monitoring of user activity
Businesses must carefully manage cloud security settings and restrict access to authorized users only.
6. Insider Threats
Not all cybersecurity threats come from outside attackers.
Employees or contractors with system access may accidentally or intentionally expose company data.
Insider threats may involve:
- Sharing confidential files
- Downloading sensitive data
- Misusing company credentials
Limiting access to critical systems and monitoring user activity helps reduce these risks.
7. Weak Password Security
Weak passwords remain one of the easiest ways for attackers to access company systems.
Common problems include:
- Using simple passwords
- Reusing passwords across multiple accounts
- Not updating passwords regularly
Implementing strong password policies and password managers can significantly improve security.
8. Internet of Things (IoT) Vulnerabilities
Many offices now use connected devices such as:
- Smart cameras
- Network printers
- Smart locks
- Connected meeting systems
If these devices are not secured properly, they can provide hackers with entry points into company networks.
All connected devices should be updated regularly and protected with strong credentials.
9. Advanced Malware Attacks
Modern malware is becoming more sophisticated and difficult to detect.
Some malware can remain hidden inside systems for months while collecting sensitive information.
Businesses should use advanced endpoint protection systems to detect and isolate threats.
10. Data Privacy and Compliance Risks
Governments around the world are introducing stricter data protection regulations.
Businesses must ensure they handle customer data responsibly and follow compliance requirements.
Failure to protect sensitive data can result in:
- Regulatory penalties
- Legal actions
- Loss of customer trust
Compliance is now a major part of cybersecurity strategy.
7 Cybersecurity Steps Every Business Should Take Today
While threats continue to evolve, several basic security practices can dramatically reduce risk.
1. Enable Multi-Factor Authentication
Multi-factor authentication adds an additional layer of protection beyond passwords.
Even if login credentials are compromised, attackers cannot access systems without additional verification.
2. Train Employees About Cybersecurity
Employees are often the first line of defense.
Training programs should teach staff how to identify phishing emails and suspicious activity.
3. Keep Software Updated
Outdated software is one of the easiest ways hackers exploit vulnerabilities.
Businesses should apply security updates and patches regularly.
4. Use Network Monitoring Tools
Network monitoring systems can detect unusual behavior such as unauthorized login attempts or data transfers.
Early detection prevents larger attacks.
5. Secure Cloud Storage
Businesses must ensure cloud platforms use encryption, strong authentication, and access restrictions.
6. Backup Business Data
Automated backups protect companies from ransomware attacks and accidental data loss.
Backups should be stored securely and tested regularly.
7. Limit Access to Sensitive Data
Employees should only have access to the systems necessary for their role.
Reducing unnecessary access lowers security risks.
Cybersecurity Checklist for Businesses
Use this quick checklist to improve your organization’s security posture.
✔ Enable multi-factor authentication
✔ Train employees to recognize phishing attacks
✔ Update software regularly
✔ Secure cloud storage access
✔ Monitor network activity
✔ Backup critical business data
✔ Implement strong password policies
✔ Protect connected devices
✔ Limit system access permissions
This checklist can significantly reduce cybersecurity risks when implemented consistently.
Frequently Asked Questions
What is the biggest cybersecurity threat in 2026?
Ransomware and phishing attacks remain among the most common threats for businesses.
Can small businesses be targeted by hackers?
Yes. Small businesses are often targeted because they may lack advanced security systems.
How often should businesses update their security systems?
Security updates should be applied as soon as they become available. Regular vulnerability scans should also be conducted.
What is Zero Trust security?
Zero Trust is a cybersecurity model where every user and device must be verified before accessing systems, even inside the company network.
How do ransomware attacks happen?
Ransomware typically spreads through malicious email attachments, compromised websites, or software vulnerabilities.
How much does a cyberattack cost a business?
Costs vary widely, but businesses may lose money through downtime, recovery expenses, legal issues, and reputation damage.
What is the best way to protect company data?
Combining strong authentication, encryption, employee training, and regular backups provides the best protection.
Strengthening Cybersecurity Through Technology and Expertise
Many businesses now rely on professional technology partners to improve security systems.
Working with experienced IT providers helps companies:
- Monitor network threats
- Secure business websites
- Protect customer data
- Maintain secure infrastructure
Many businesses partner with professional IT service providers such as DOC Infotech to implement advanced cybersecurity protection and monitor threats in real time.
Conclusion
Cybersecurity threats are evolving rapidly, and businesses must adapt to stay protected.
Ignoring digital security can lead to serious consequences, including financial losses, operational disruption, and damaged customer trust.
However, organizations that invest in modern security tools, educate employees, and follow strong protection strategies can significantly reduce their risk.
Cybersecurity is no longer optional.
It is a critical investment in the future stability, reputation, and success of your business.